The use of Laptops, mobile phones, and USB flash drives is now more common than ever. Especially the portability of these devices makes them extremely popular amongst the general public and business users alike.
However, these systems typically contain vast quantities of confidential details. Should this data get into the wrong hands, it could lead to the unauthorized exposure of confidential, classified, or sensitive data, theoretically affecting the organizations with a loss of billions of dollars.
There is one solution to all these issues, which is encryption.
If you are familiar with data encryption, you must have heard of TrueCrypt, the most popular encryption software since 2004 until its demise in 2014.
Tools such as TrueCrypt primarily help in building encrypted partitions on any provided hard drive. Besides, you can also use them to create simulated encrypted disks that reside in a given format.
If a user has completed the encryption operation, no one can access the encrypted data stored on any given partition without the required password, which only the user can access. These features led to TrueCrypt’s popularity at the time of its initial release in 2004.
Many of you may feel doomed as TrueCrypt is no longer available. But this article puts an end to your worries by presenting the best alternatives to Truecrypt.
Quick list of Truecrypt alternatives
Short on time to read the full guide? Don’t worry. Let’s begin with encrypting your data with these Truecrypt substitutes.
- Veracrypt – an open-source Truecrypt fork available for free.
- Bitlocker – a full-disk encryptor limited to Windows only.
- DiskCryptor – free and open-source tool offering fast encryption.
- CipherShed – a Truecrypt fork offering multi-platform support
- Axcrypt – a freemium encryption resource with user-friendly features.
What went wrong with Truecrypt?
Most of us recognize TrueCrypt as a fantastic free and open-source hardware encryption utility. The project surfaced online in 2004 as a standalone real-time encryption tool.
However, TrueCrypt did not make it past its 10th anniversary as the developers discontinued it in 2014. But no one knows the reason(s) behind it because the developers had remained anonymous and made no further announcements in this regard.

What made TrueCrypt popular was its ability to build encrypted partitions on any provided hard drive. Also, companies would use it to create virtual encrypted disks that reside in a given file.
Moreover, the tool offered diversified compatibility with almost all popular operating systems such as Windows and macOS.
Some people hold Google’s Project Zero security team responsible for the end of TrueCrypt’s reign. The team found numerous security bugs unknown to the public in TrueCrypt’s encryption algorithm.
Nevertheless, a 77-page study from the Fraunhofer Institute for Secure Information Technology in 2015, which conducted a systematic audit of TrueCrypt’s latest stable version, found the software fit to encrypt specific drives, specifically data encryption on an external hard drive or USB drive.
It means that if present on an external hard drive, the encrypted data was reasonably secure. However, TrueCrypt was not given the green light if the encrypted data remained on a fixed drive or the system’s main memory.
Anyhow, the bottom line is TrueCrypt is gone. It is no longer being maintained or patched for bugs. This makes it possible to retrieve the key from the unmounted drive and use it to decrypt data.
Moreover, the developers no longer provide the source files. You can now only download it through unofficial piracy sites. Albeit, doing so has its own risks, such as exposure to corrupted or malicious files.
Is it still safe to use TrueCrypt?
As elaborated above, TrueCrypt was discontinued in 2014, which means it’s been years since its development team decided not to fix any flaws or bugs within the software.

Whereas, downloading the tool from piracy platforms also poses security risks, as mentioned earlier.
Another alternative to pirating is using the GitHub repository, which claims to host a legit version of TrueCrypt Download 7.1. However, it is a mere claim from The Open Crypto Project with no concrete evidence to back it up.
TrueCrypt may still be of some use for processing the original files that you have had since before the discontinuation. But this is only helpful if you are using it to encrypt data on external drives, and your system is reasonably old.
In brief, the safety of using Truecrypt today depends on what system you are using it on, what drive you are encrypting, and your understanding of the underlying risks of data corruption through pirated source files.
Ideally, do not use TrueCrypt any further unless you utilize it to migrate existing data encrypted by TrueCrypt.
Top 3 encryption methods
Before moving on to the Truecrypt alternatives, let’s quickly look at the basic data encryption methods that these tools apply to secure your data.
1. Full-disk encryption
Many operating systems store temporary files/swap partitions on hard drives. Because these files hold confidential data, potential compromises here can give rise to various issues.
Thus, encrypting the entire hard drive comes as a quick solution to avoid this problem. Full Disk Encryption (FDE) methods, often known as “On-Disk Encryption” or “Complete Disk Encryption,” operate by encrypting every single piece of data on a storage system that exists.
The full-disk encryption method usually encrypts the entire content of a disk or volume. It then decrypts/encrypts it after a key has been issued during usage. This ensures the data remains safe under any circumstances, such as the laptop/disk failure or hacking attack where the data gets encrypted, and you need a key for decryption.
However, this type of encryption makes your data vulnerable to online threats. It means that if the device is logged in or the data is being sent through an email, you cannot provide any form of encryption.
2. Single-user file/folder level encryption
Most encryption programs are capable of creating an encrypted internet drive. This is what folder-level encryption does. It creates a virtual disk, an encrypted file that looks like any other drive on your device. This allows the user to easily open and transfer files in an encrypted region.
This encryption method is useful for protecting a single file and folder rather than your whole disk. For example, you can use it to protect a specific folder containing sensitive information that only you can only access in the case of a hacking attack or device theft.
3. Multi-user file/folder level encryption
Like single-user file encryption, multi-user file/folder level encryption also creates a virtual drive to keep encrypted files. The only difference here is that this encryption mode allows multiple users to access encrypted information simultaneously.
However, you need to be careful when using this method. This methodology becomes complicated if not all users have the encryption program installed. In addition, any errors here may cause users to access encrypted data or lead them to think they have encrypted information when they have not falsely.
The types of encryption most widely known and used are:
5 best TrueCrypt alternatives
Unfortunately, TrueCrypt has not received any patches in recent years. Nor is it publicly available for download anymore. So does it mean your data would remain vulnerable? Not really.
Many alternatives are available today that provide services similar to TrueCrypt, if not better. Regarding which one is the best depends on various factors. Mainly, what counts here is the type of encryption method you want, your device operating system, and other similar factors.
Nonetheless, whatever your intended purposes may be, the following best Truecrypt alternatives will indeed serve you well.
1. Veracrypt
VeraCrypt can manage about anything you throw at it; it is free, open-source, and multiplatform. It is a fork of TrueCrypt. (A project fork occurs when programmers copy the source code from a specific software platform and start working independently on it, making a new software piece.)
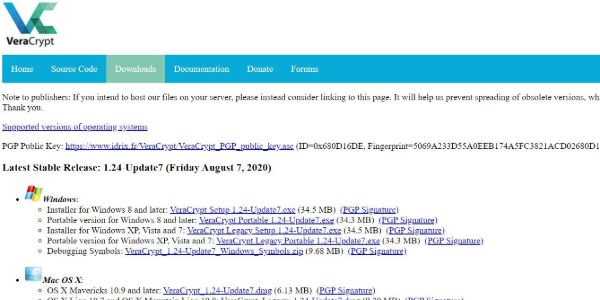
VeraCrypt works on AES (advanced encryption standard), TwoFish, and Serpent encryption ciphers to protect your data. It allows full disk encryption, including device drive encryption, along with encrypting volumes within volumes.
The tool works on all operating systems and their versions. Notably, it stands as one of the best TrueCrypt Mac alternatives for Apple fanatics.
VeraCrypt is marginally slower in terms of starting and opening containers than TrueCrypt. But it does not hinder the use of apps anyway. You can navigate through VeraCrypt’s official website to read over all the latest features it provides. There is also a separate page where the VeraCrypt team explains how different their app is from TrueCrypt.
To keep sensitive files and data secure or to encrypt the whole system, Veracrypt is the versatile go-to option. It can manage both volume encryption and on-the-fly encryption so that only approved users can access them, making VeraCrypt the most popular software after TrueCrypt.
2. Bitlocker
Bitlocker is Microsoft’s very own encryption tool. However, it is not open-source and only runs on Windows Ultimate, Pro, or Enterprise versions.
Just as VeraCrypt, Bitlocker also supports advanced encryption standards. It mainly supports full-disk encryption to protect your entire computer and not just individual files. It also works for encrypting a virtual drive or other volumes that you can view and access like other drives on your computer.
One downside of Bitlocker is that not everybody has access to the Windows models of Pro or Enterprise, which renders Bitlocker a no-hope for many. If you have Home versions for Windows, you would have to give up the thought of using Bitlocker altogether.
3. DiskCryptor
DiskCryptor, much like TrueCrypt, is a free, open-source file and drive encryption program. As with TrueCrypt, DiskCrypror would encrypt all of your data, system drives alongside other external devices, such as CD and USB drives.
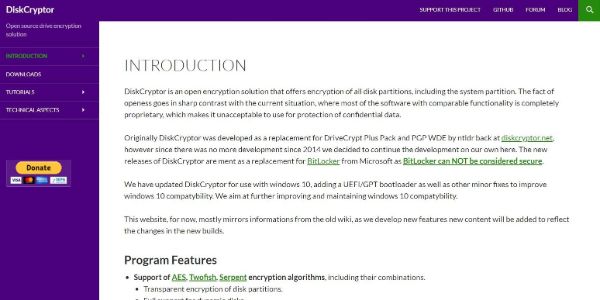
DiskCryptor bears striking similarities to TrueCrypt – thanks to an anonymous TrueCrypt user who initiated this project as an alternative.
Although, like TrueCrypt, DiskCryptor also seemingly discontinued in 2014. However, it later resumed in 2020 and is now actively maintained. (Though it remains unclear if the new maintainer is the same or related to the original developer.)
Anyhow, you can also download it through SourceForge.
DiskCryptor is incredibly fast and convenient to use. It does not use much computing power and encrypts files faster than TrueCrypt would. Like VeraCrypt, DiskCryptor encrypts your data with multiple encryption algorithms, including Advanced Encryption Standard, Serpent, and Twofish, for increased security.
The main downside to DiskCryptor is that while it is open-source, close to no individuals or organizations have conducted any notable security analysis of it.
4. CipherShed
CiperShed had its humble beginnings as a fork of TrueCrypt. It supports different operating systems, such as Windows, Linux, and macOS. Although to use it on Linux and Mac, you would have to compile the program.

The first non-alpha version arrived in February 2016. After its initial release, CipherShed’s progress has noticeably lagged compared to VeraCrypt, since there was no official major release such as v1.0. Even after years, the current CipherShed version still appears v.0.7.4.0.
CipherShed offers most, if not all, resources close to VeraCrypt, despite how slow its growth is.
5. Axcrypt
Next on our list of TrueCrypt alternatives is also an open-source, cross-platform per-file encryption software that secures files by supporting AES and requires zero configurations.
While Windows users can enjoy a free version, users with macOS must get a premium edition, retailing at USD 35 annually.

For encrypting a file using AxCrypt, right-click on it and pick the encrypt option. And voila! The tool will automatically encrypt your file with AES–128-bit encryption. This is the most straightforward encryption software to use amongst all mentioned in this list.
This also means that Axcrypt does not provide the feature of full drive encryption.
Another major downside to using AxCrypt is that you miss out on cross-platform compatibility if you are availing of the free version. However, you can solve this by opting for the premium version with a 30-day free trial.
Using a VPN for encrypting transiting data
Is disk encryption enough to secure your files sent via email? The straightforward answer is No.
Disk encryption protects your data only while it resides on your device or hard drive but does not secure it when transmitted over the internet. So you need a VPN (Virtual Private Network) for that.

Using a VPN encrypts your data in transit, thereby becoming indecipherable for intruders. Hackers typically use some network sniffer to sniff networks for usernames and passwords, which means your data is at risk of theft at all times. However, by using a VPN, you ensure the security of your data.
A VPN operates by redirecting your system’s internet connection through your chosen VPN server instead of letting it through your ISP. Hence, it appears that your data is being transmitted from the VPN instead of your system. For example, you could be in the United Kingdom and using an IP address found in the United States. Basically, by adopting a VPN, you are hiding in plain sight.
Nonetheless, bear in mind that not all VPNs are equal. Different services offer various speeds, capabilities, or even vulnerabilities depending on the protocols they use.
Therefore, you should only use a VPN tested for security. Precisely, pick a VPN service provider that supports VPN protocols like IKEv2, SoftEther, and OpenVPN, and ciphers like Camilla and AES. You may also idealize VPNs that offer handshake encryption, such as RSA-2048 and authentication encryption, over 256 bits.
To save your time and energy, check out this guide listing the 10 best VPNs. It features the top secure and reliable providers out there. Of course, you are welcome and encouraged to do your very own research before settling with a VPN.
Final thoughts
While TrueCrypt is gone, there are many alternatives to TrueCrypt that provide services similar to it. That said, the ones listed above will surely meet your encryption requirements.
A key thing to highlight here is the feature that most encryption software proudly boasts – plausible deniability.
Briefly, when it comes to disk encryption, plausible deniability refers to the fact that no one can prove that there is any form of encrypted data on your computer. That is because encrypted data looks the same as no data at all – it is all hidden in plain sight.
Therefore, when looking for any Truecrypt alternatives to secure your data, don’t fall for this claim from the providers.
There is still considerable debate on whether encryption can be used to claim plausible deniability in the court of law. Thus, do not choose your encryption software based on its plausible denial mechanism. It is like having a great strategy but weak gameplay, resulting in the whole game going into the gutter.
Instead, pick the one that best matches your data encryption requirements with no security threats.
Images via Pixabay.